API Keys, JWT, OAuth
- 2021年10月18日
- Web Service
There are many authentication & authorization mechanisms to protect and restrict our APIs nowadays. Today I will talk about the three popular mechanisms among them.
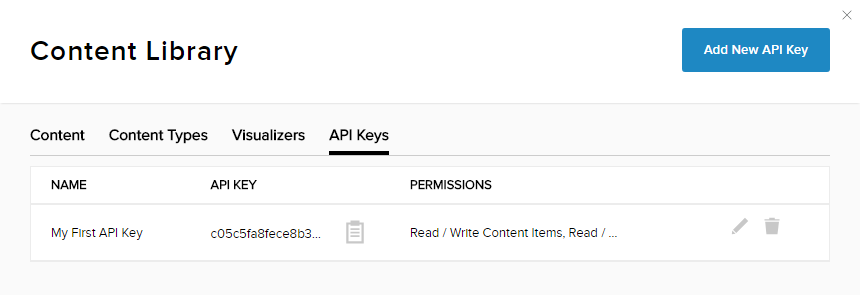
API Keys
In the early days, API keys were the only option for limiting or tracking API traffic. The best thing about API keys is their simplicity. All you have to do is log in to the service, find its API key and use it in future requests for authentication. However, along with simplicity, there are drawbacks to API key security and user experience. If the API key grants full access to all operations that the API can perform, such as writing new data or deleting existing data, then the API key occurs and it is harmful for an attacker to know it. .. We recommend that you include your API key in the Authorization header when submitting your request.
JWT
I also talked about JWT in previous weeks. If you want to read more detail, you can check it out my previous articles.
JSON Web Token (JWT) can be used in a variety of scenarios. You can use a JWT access token to avoid database lookups because the JWT contains the base64-encoded version of the data needed to determine the identity and scope of the access. The JWT also contains signatures calculated using JWT data, creating own version of the signature using the same secret you used to create the JWT. This calculation is much more efficient than looking up the access token in the database to determine who it belongs to and whether it is valid. The JWT token must also be passed in the Authorization header. The disadvantage is that you can’t revoke the JWT on its own. Therefore, we recommend that you use JWT in combination with JWT refresh tokens and expiration tokens. If you want to improve security, you need to check the JWT signature for each API call to make sure that the expiration date is still valid.

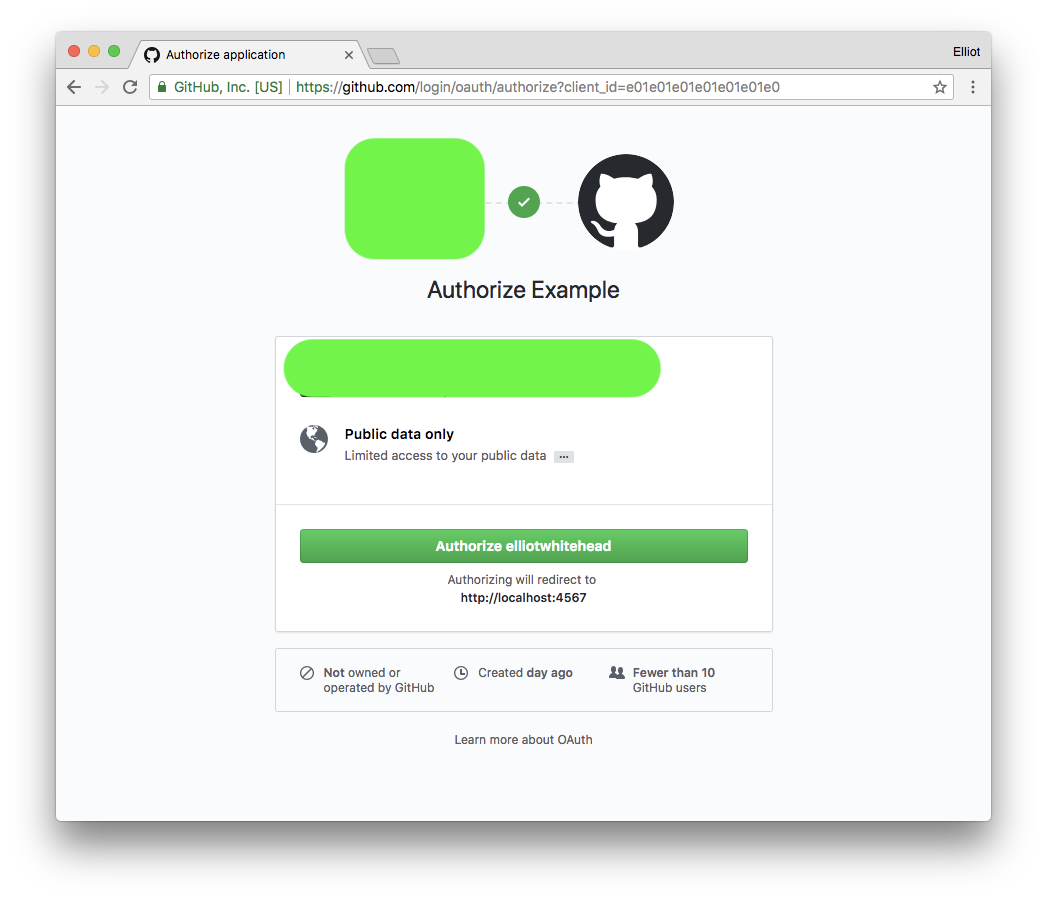
OAuth
OAuth is the answer to communicate and access user data between services. Unlike API keys, OAuth does not require users to access the developer portal, settings, and so on. In fact, users can access their account with the a simple one click. The most common OAuth implementation uses one or both of the following tokens as below.
Access Token – Sent as an API key, allowing the application to access your data. Optionally, the access token can expire.
Refresh Token: Optional part of the OAuth flow, the renewal token gets a new access token if it has expired. The place where you are most likely to put it is also the authentication header.
Same with API keys, anyone with an access token can invoke harmful operations, such as deleting data. However, OAuth offers some improvements over API keys, like you can associate an access token with a specific scope. This limits the operations and types of data that the application can access so called permission. Also, when combined with a renewal token, the access token expires, which can limit negative impact. Finally, the access token can be revoked even if the refresh token is not in use.
Conclusion
Use API keys if you expect developers to build internal applications that do not need to access data from multiple users.
Use JWT in combination with OAuth if you want to limit database lookups but don’t need the ability to immediately revoke access.
Use OAuth access tokens if you want users to be able to easily authorize services without having to share private data or complicated works.
yuuma at 2021年10月18日 10:15:00